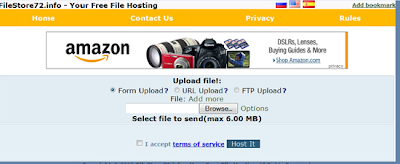
Filestore72.info is one of a variant of browser hijacker than injects within users PC silently and create chaos by redirecting each and every single users web link to it's sponsored http://filestore72.info website. However the basic motto of filestore72.info redirect virus is to promote the filthy products of it's customers in better works the hackers and generate revenue for them. Apart from upraising browser redirection issue it also set's the sponsored website as the default homepage or search engine of the compromised system.
Therefore if you are making the same mistake by considering filestore72.info as a legit free hosting website then drop that though then and there as it is nothing more than a malicious redirect virus. Hence look for genuine solutions to find and remove filestore72.info thoroughly from the infected PC.
Therefore if you are making the same mistake by considering filestore72.info as a legit free hosting website then drop that though then and there as it is nothing more than a malicious redirect virus. Hence look for genuine solutions to find and remove filestore72.info thoroughly from the infected PC.
Threat Assessment
Type – Trojan
Geographical Distribution- Global
Alert Level – Severe
Difficult Level to Solve Filestore72.info – 7
No of Files Infected – 0-25
Countries Affected – China, North America, Western Europe
System Infected – Windows 95, 98, 2000, 2003 Server, XP, Vista, and Windows 7
Filestore72.info penetrate within targeted computer through several illicit means like:
- Peer-to-Peer file sharing network
- Fake video codec download
- Visiting malicious websites
- Bundled with spam emails or attachments
- Freeware or shareware download
- Via secondary storage media such as USB
Automatic Method to Remove Filestore72.info
You must not ignore the threat as it's presence within your system for long can cause severe damage to it. Therefore for instant removal of Filestore72.info use an Automatic Filestore72.info Removal Tool. The high ending scanning algorithm of the tool exhaustively scan the infected system thus detecting and removing Filestore72.info completely. The biggest advantage associated with the tool is that it does not require user to be technically strong enough in order to install and run the removal tool within their PC
You must not ignore the threat as it's presence within your system for long can cause severe damage to it. Therefore for instant removal of Filestore72.info use an Automatic Filestore72.info Removal Tool. The high ending scanning algorithm of the tool exhaustively scan the infected system thus detecting and removing Filestore72.info completely. The biggest advantage associated with the tool is that it does not require user to be technically strong enough in order to install and run the removal tool within their PC
Recommendations to Protect PC from Future worm Attacks
- Keep operating system updated
- Use powerful system security tool
- Install firewall
- Be alert while opening emails or attachments
- Avoid freeware or shareware download
- Make use of strong password and
- Be careful while removing removable devices
- Stay connected with Security Websites

No comments:
Post a Comment